Internet of Things Protocols | IoT Communication Model and APIs
In this article we discuss Internet of Things Protocols, IoT Communication Model and APIs. Internet of Things Protocols help to establish Communication between IoT Device (Node Device) and Cloud based Server over the Internet. It help to sent commands to IoT Device and received data from an IoT device over the Internet.
We expain some most popular Internet of Things Protocols in this article. Here we diveded Internet of Things Protocols into IoT Data Protocols and Wireless Iot Network Protocols. This is not classification of IoT Protocols, Read this for understanding Internet of Things Protocols : https://iotbyhvm.ooo/physical-and-logical-design-of-iot/
Internet of Things Protocols
IoT Data Protocols – Internet of Things Protocols
Some Popular IoT Data Protocols is – MQTT, CoAP and AMQP.
Constrained Application Protocol (CoAP) – Internet of Things Protocols
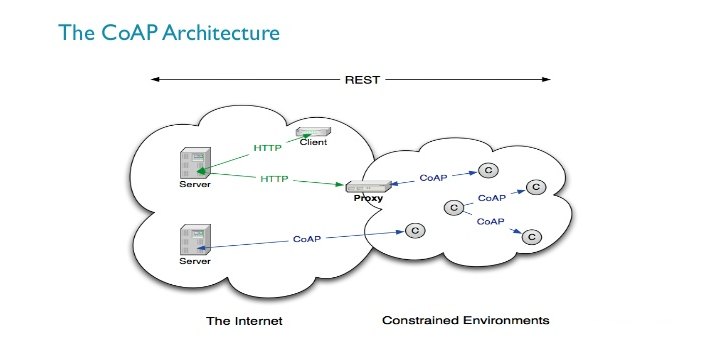
The CoAP protocol is specified in RFC 7252. The Constrained Application Protocol (CoAP) is a specialized web transfer protocol for use with constrained nodes and constrained networks in the Internet of Things.
Coap is designed for machine-to-machine (M2M) applications such as smart energy and building automation. The protocol is targetted for Internet of Things (IoT) devices having less memory and less power specifications.
On top of CoAP, the Open Mobile Alliance (OMA) has defined “Lightweight M2M” as a simple, low-cost remote management and service enablement mechanism.
Following are the features of CoAP Protocol:
• It is very efficient RESTful protocol.
• Easy to proxy to/from HTTP.
• Open IETF standard
• Embedded web transfer protocol (coap://)
• It uses asynchronous transaction model.
• UDP is binding with reliability and multicast support.
• GET, POST, PUT and DELETE methods are used.
• URI is supported.
• It uses small and simple 4 byte header.
• Supports binding to UDP, SMS and TCP.
• DTLS based PSK, RPK and certificate security is used.
• uses subset of MIME types and HTTP response codes.
• Uses built in discovery mechanism.
Read more: COAP vs MQTT | Difference between COAP and MQTT protocols | CoAP Protocol- Constrained Application Protocol
Message Queuing Telemetry Transport Protocol (MQTT) – Internet of Things Protocols
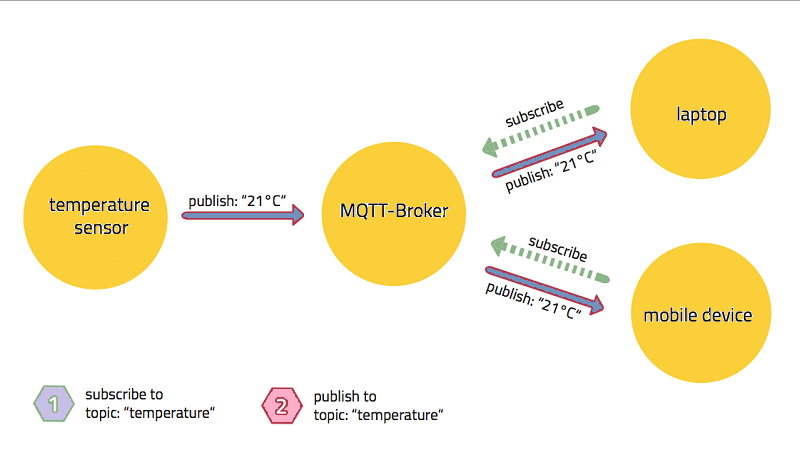
MQTT is a machine-to-machine (M2M)/”Internet of Things” connectivity protocol. It was designed as an extremely lightweight publish/subscribe messaging transport and useful for connections with remote locations where a small code footprint is required and/or network bandwidth is at a premium. For example, it has been used in sensors communicating to a broker via satellite link, over occasional dial-up connections with healthcare providers, and in a range of home automation and small device scenarios.
MQTT protocol runs on top of the TCP/IP networking stack. When clients connect and publish/subscribe, MQTT has different message types that help with the handshaking of that process. The MQTT header is two bytes and first byte is constant. In the first byte, you specify the type of message being sent as well as the QoS level, retain, and DUP (duplication) flags. The second byte is the remaining length field.
Features of MQTT?
- Distribute information more efficiently
- Increase scalability
- Reduce network bandwidth consumption dramatically
- Reduce update rates to seconds
- Very well-suited for remote sensing and control
- Maximize available bandwidth
- Extremely lightweight overhead
- Very secure with permission-based security
- Used by the oil-and-gas industry, Amazon, Facebook, and other major businesses
- Saves development time
- Collects more data with less bandwidth compared to polling protocols
If you’re new to messaging protocols visit this : MQTT | What is MQTT | MQTT in Depth | QoS | FAQs | MQTT Introduction
Recommended: MQTT Servers/Brokers | MQTT Public Brokers List | MQTT 5 | Overview | What’s New | MQTT Features | MQTT 5.0
Advanced Message Queuing Protocol (AMQP) – Internet of Things Protocols
The AMQP – IoT protocols consist of a hard and fast of components that route and save messages within a broker carrier, with a set of policies for wiring the components together. The AMQP protocol enables patron programs to talk to the dealer and engage with the AMQP model. AMQP has the following three additives, which might link into processing chains in the server to create the favored capability.
- Exchange: Receives messages from publisher primarily based programs and routes them to ‘message queues’.
- Message Queue: Stores messages until they may thoroughly process via the eating client software.
- Binding: States the connection between the message queue and the change.

Wireless IoT Network Protocols – Internet of Things Protocols
Bluetooth
Bluetooth is a global 2.4 GHz personal area network for short-range wireless communication. Device-to-device file transfers, wireless speakers, and wireless headsets are often enabled with Bluetooth.
BLE
BLE is a version of Bluetooth designed for lower-powered devices that use less data. To conserve power, BLE remains in sleep mode except when a connection is initiated. This makes it ideal for wearable fitness trackers and health monitors.
ZigBee
(Narrow-Band IoT) A technology being standardized by the 3GPP standards bodyThe ZigBee protocol uses the 802.15.4 standard and operates in the 2.4 GHz frequency range with 250 kbps. The maximum number of nodes in the network is 1024 with a range up to 200 meter. ZigBee can use 128 bit AES encryption.
Z-Wave
Z-Wave is a sub-GHz mesh network protocol, and is a proprietary stack. It operates in the sub-1GHz band and is impervious to interference from WiFi and other wireless technologies in the 2.4-GHz range such as Bluetooth or ZigBee. It’s often used for security systems, home automation, and lighting controls.
6LoWPAN
6LoWPAN is an acronym of IPv6 over Low power Wireless Personal Area Networks. It is an adaption layer for IPv6 over IEEE802.15.4 links. This protocol operates only in the 2.4 GHz frequency range with 250 kbps transfer rate. IPv6, is an Internet Layer protocol for packet-switched internetworking and provides end-to-end datagram transmission across multiple IP networks. It is an open IoT network protocol like ZigBee, and it is primarily used for home and building automation.
Thread
Built on open standards and IPv6 technology with 6LoWPAN as its foundation. You could think of it as Google’s version of ZigBee. You can actually use some of the same chips for Thread and ZigBee, because they’re both based on 802.15.4.
WiFi-ah (HaLow)
Designed specifically for low data rate, long-range sensors and controllers, 802.11ah is far more IoT-centric than many other WiFi counterparts.
2G (GSM)
2G is the “old-school” TDMA (usually) cellular protocol. ATMs and old alarm systems used this— and in most parts of the world it is phased out or in the process of being phased out.
3G & 4G
3G was the first “high speed” cellular network, and is a name that refers to a number of technologies that meet IMT-2000 standards. 4G is the generation of cellular standards that followed 3G, and is what most people use today for mobile cellular data. You can use 3G and 4G for IoT devices, but the application needs a constant power source or must be able to be recharged regularly.
LTE Cat 0, 1, & 3
With LTE classes, the lower the speed, the lower the amount of power they use. LTE Cat 1 and 0 are typically more suitable for IoT devices.
LTE-M1
This is the first cellular wireless protocol that was build from the ground up for IoT devices. That being said, it isn’t available yet, so how it performs remains to be seen.
With LTE, it’s worth understanding that carriers typically don’t have to modify hardware for their basestations; upgrades can be done entirely through software. This really helps with infrastructure costs, because companies won’t necessarily need new cellular basestations, just new endpoint hardware.
NB-IoT
(Narrow-Band IoT) A technology being standardized by the 3GPP standards body is another way to tackle cellular M2M for low power devices. It is based on a DSSS modulation similar to the old Neul version of Weightless-W. Huawei, Ericsson, and Qualcomm are active proponents of this protocol and are involved in putting it together.
5G
Though it likely won’t be released for another five years, 5G is set to be the next generation of cellular network protocol. It’s designed for high throughput, and it will probably face the same issues as 3G and 4G in regards to IoT.
NFC
NFC,is the acronym for Near Field Communication.It is a short-range high frequency wireless communication technology that enables the exchange of data between devices.It enables two electronic devices, one of which is usually a portable device such as a smartphone, to establish communication by bringing them within 4 cm (1.6 in) of each other.
RFID
Radio-frequency identification (RFID) uses electromagnetic fields. RFID is not new since it has been used almost in every industry to identify and track tags attached to objects automatically. The tags stores information electronically. There are two types of RFID tags, Active and Passive. Passive tags collect energy from RFID reader’s radio waves whereas Active tags have its power source such as a battery and can operate at hundreds of meters distance from the RFID reader. RFID technology can be used in the IoT to identify objects and link them to the Internet.
SigFox
igfox uses free ISM band to transmit data over the very narrow spectrum. Sigfox is designed to handle low data-transfer speeds of 10 to 1,000 bps using an Ultra Narrow Band (UNB) technology. Sigfox overcomes the problem of Wi-Fi and cellular in many applications that has short Wi-Fi range, where cellular cost is high and consumes more power.
SIGFOX is a French company that builds wireless networks, which is founded in 2009 by Ludovic Le Moan and Christophe Fourtet. Typically, it is an internet of things device that needs to transmit continuously in small amount data. Best use cases for Sigfox are electricity meters, smart watches, and washing machines.
LoRaWAN
Network protocol intended for wireless battery operated Things in regional, national or global network. LoRaWAN is a media access control (MAC) layer protocol designed for large-scale public networks with a single operator. It is built using Semtech’s LoRa modulation as the underlying PHY, but it is important to note that LoRa and LoRaWAN are two seperate things that are often (mistakenly) conflated.
Ingenu
Ingenu has created something called random phase multiple access (RPMA), which uses Direct Sequence Spread Spectrum (DSSS) and is similar to code division multiple access (CDMA) cellular protocols. Before IoT was a thing, Ingenu (then OnRamp) was selling metering infrastructure that collected low power information from electricity meters. Now, it’s rebranded and is trying to become a broader player in the field (like SigFox).
Weightless-N
Weightless-N is an ultra narrowband system that is very similar to SigFox. Instead of being a complete end-to-end enclosed system, it’s made up of a network of partners. It uses differential binary phase shift keying (BPSK) in narrow frequency channels and is intended for uplink sensor data.
Weightless-P
Weightless-P is the latest Weightless technology. It offers two-way features and quality of service tiers, which we think is very important.
Weightless-W
Weightless-W is an open standard designed to operate in TV white space (TVWS) spectrum. Using TVWS is attractive in theory, because it takes advantage of good ultra high frequency (UHF) spectrum that’s not otherwise in use—but it can be quite difficult in practice.
ANT & ANT+
If you have a Samsung device, you probably have a radio with their protocol in it. ANT & ANT+ seem somewhat like another type of BLE system, designed to create networks that piggyback off of existing hardware. A lot of devices have ANT or ANT+ compatible chips in them, and the idea is that if you get enough of these radios added to the world, you can use them together as a mesh.
DigiMesh
DigiMesh is one of a number of proprietary mesh systems. You can learn about the differences between it and ZigBee in this white paper.
MiWi
MiWi is Microchip’s proprietary network protocol. It was created for short-range networks and designed to help customers reduce their products’ time to market.
EnOcean
EnOcean is a an energy harvesting wireless technology which works in the frequencies of 868 MHz for europe and 315 MHz for North America. The transmit range goes up to 30 meter in buildings and up to 300 meter outdoor. Thus, its applications are centered around building automation, smart homes, and wireless lighting control.
Dash7
Dash7 is an open-source wireless network protocol with a huge RFID contract with the U.S. Department of Defense.
WirelessHART
WirelessHART is built on the HART Communication Protocol, and is what the company considers “the industry’s first international open wireless communication standard.”
Communication / Transport layer
Anyhow if you are aware of any protocols that are relevant in this context not listed here, please feel free to mention them in the comments below.
IoT Communication APIs
Generally we used Two APIs For IoT Communication. These IoT Communication APIs are:
- REST-based Communication APIs
- WebSocket-based Communication APIs
REST-based Communication APIs
Representational state transfer (REST) is a set of architectural principles by which you can design Web services the Web APIs that focus on systems’s resources and how resource states are addressed and transferred. REST APIs that follow the request response communication model, the rest architectural constraint apply to the components, connector and data elements, within a distributed hypermedia system. The rest architectural constraint are as follows:
Client-server – The principle behind the client-server constraint is the separation of concerns. for example clients should not be concerned with the storage of data which is concern of the serve. Similarly the server should not be concerned about the user interface, which is concern of the clien. Separation allows client and server to be independently developed and updated.
Stateless – Each request from client to server must contain all the information necessary to understand the request, and cannot take advantage of any stored context on the server. The session state is kept entirely on the client.
Cache-able – Cache constraints requires that the data within a response to a request be implicitly or explicitly leveled as cache-able or non cache-able. If a response is cache-able, then a client cache is given the right to reuse that repsonse data for later, equivalent requests. caching can partially or completely eliminate some instructions and improve efficiency and scalability.
Layered system – layered system constraints, constrains the behavior of components such that each component cannot see beyond the immediate layer with they are interacting. For example, the client cannot tell whether it is connected directly to the end server or two an intermediaryalong the way. System scalability can be improved by allowing intermediaries to respond to requests instead of the end server, without the client having to do anything different.
Uniform interface – uniform interface constraints requires that the method of communication between client and server must be uniform. Resources are identified in the requests (by URIsin web based systems) and are themselves is separate from the representations of the resources data returned to the client. When a client holds a representation of resources it has all the information required to update or delete the resource you (provided the client has required permissions). Each message includes enough information to describe how to process the message.
Code on demand – Servers can provide executable code or scripts for clients to execute in their context. this constraint is the only one that is optional.
A RESTful web service is a ” Web API ” implemented using HTTP and REST principles. REST is most popular IoT Communication APIs.
| Uniform Resource Identifier (URI) | GET | PUT | PATCH | POST | DELETE |
|---|---|---|---|---|---|
Collection, such as https://api.example.com/resources/ |
List the URIs and perhaps other details of the collection’s members. | Replace the entire collection with another collection. | Not generally used | Create a new entry in the collection. The new entry’s URI is assigned automatically and is usually returned by the operation. | Delete the entire collection. |
Element, such as https://api.example.com/resources/item5 |
Retrieve a representation of the addressed member of the collection, expressed in an appropriate Internet media type. | Replace the addressed member of the collection, or if it does not exist, create it. | Update the addressed member of the collection. | Not generally used. Treat the addressed member as a collection in its own right and create a new entry within it. | Delete the addressed member of the collection. |
WebSocket based communication API
Websocket APIs allow bi-directional, full duplex communication between clients and servers. Websocket APIs follow the exclusive pair communication model. Unlike request-response model such as REST, the WebSocket APIs allow full duplex communication and do not require new coonection to be setup for each message to be sent. Websocket communication begins with a connection setup request sent by the client to the server. The request (called websocket handshake) is sent over HTTP and the server interprets it is an upgrade request. If the server supports websocket protocol, the server responds to the websocket handshake response. After the connection setup client and server can send data/mesages to each other in full duplex mode. Websocket API reduce the network traffic and letency as there is no overhead for connection setup and termination requests for each message. Websocket suitable for IoT applications that have low latency or high throughput requirements. So Web socket is most suitable IoT Communication APIs for IoT System.

IoT Communication Models
Request-Response Model
Request-response model is communication model in which the client sends requests to the server and the server responds to the requests. When the server receives a request, it decides how to respond, fetches the data, retrieves resource representation, prepares the response, and then sends the response to the client. Request-response is a stateless communication model and each request-response pair is independent of others.
HTTP works as a request-response protocol between a client and server. A web browser may be the client, and an application on a computer that hosts a web site may be the server.
Example: A client (browser) submits an HTTP request to the server; then the server returns a response to the client. The response contains status information about the request and may also contain the requested content.

Publish-Subscribe Model
Publish-Subscribe is a communication model that involves publishers, brokers and consumers. Publishers are the source of data. Publishers send the data to the topics which are managed by the broker. Publishers are not aware of the consumers. Consumers subscribe to the topics which are managed by the broker. When the broker receive data for a topic from the publisher, it sends the data to all the subscribed consumers.

Push-Pull Model
Push-Pull is a communication model in which the data producers push the data to queues and the consumers Pull the data from the Queues. Producers do not need to be aware of the consumers. Queues help in decoupling the messaging between the Producers and Consumers. Queues also act as a buffer which helps in situations when there is a mismatch between the rate at which the producers push data and the rate rate at which the consumer pull data.

Exclusive Pair Model
Exclusive Pair is a bidirectional, fully duplex communication model that uses a persistent connection between the client and server. Connection is setup it remains open until the client sends a request to close the connection. Client and server can send messages to each other after connection setup. Exclusive pair is stateful communication model and the server is aware of all the open connections.

Thanks for reading. If you like this post “Internet of Things Protocols, Communication Model and APIs” probably you might like my next ones, so please support me by subscribing my blog.You may also like:


Pingback: What is an API ? | Making Things Easier for Developers
Pingback: What is IoT ? | Internet of Things - IoTbyHVM - Bits & Bytes of IoT
Pingback: espcom_sync_failed [ERROR Solved] - IoTbyHVM - Bits & Bytes of IoT